Growing technologies are making both attacks and prevention techniques more and more sophisticated. These technologies have made both adversaries and security professionals engage in a rat race. Attackers try every possible method to evade detection, while security professionals strive to thwart their attempts. Therefore, for a security professional, it is not optional to learn evasion techniques; it is a must. Although we can’t cover all evasion techniques in one post, we believe that by learning these three common types of process-based attacks used by malware programs to evade detection, you will be able to understand and detect many cyber attacks and create a strategy to protect your resources.
In this post, we will cover the most common attacks targeting system processes by malicious programs. They are:
- Process Injection
- Process Hallowing
- Process Doppelganging
Process Injection: A Stealthy Code Maneuver
Process injection is an infiltration technique commonly used by cybercriminals and malware to evade detection and execute malicious code stealthily on targeted systems. In this section, we will cover what process injection is, how it works, the various techniques used, why attackers leverage it, and most importantly – how to defend against process injection attacks.
What is Process Injection?
Process injection refers to a technique where malicious code is forced to run within the address space of another legitimate process. The key aspect is that the malicious code executes under the disguise of a trusted process to avoid detection.
By injecting into legitimate processes, the malicious code can bypass security mechanisms that monitor new process creation. It also inherits the permissions of the target process and can access system resources. This makes process injection a popular tactic for malware, hackers, and pen testers.
How Process Injection Works: A Step-by-Step Guide?
The steps involved in a typical process injection attack are:
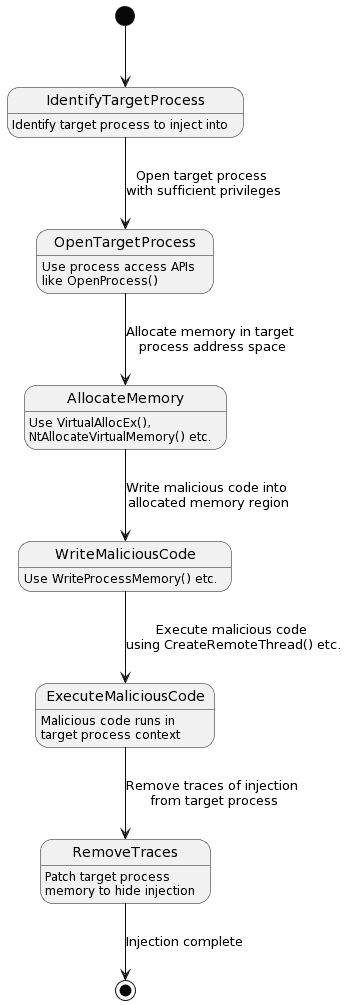
- Identify a target process to inject into. This is usually a critical system process that is likely to be running like
svchost.exe,explorer.exeetc. - Use process access APIs to open the target process with sufficient privileges. Common APIs used are
OpenProcess()orNtOpenProcess(). - Allocate memory in the target process’s address space. This can be done via
VirtualAllocEx()orNtAllocateVirtualMemory(). - Write the malicious code into the allocated memory region inside the target process. APIs like
WriteProcessMemory()help achieve this. - Execute the malicious code using thread execution APIs like
CreateRemoteThread()orRtlCreateUserThread(). - The injected code now runs surreptitiously inside the target process’s context achieving the attacker’s objectives.
- The injected code patches the target process’s memory to remove traces and any evidence of injection.
This allows the malware to stealthily execute while impersonating a legitimate system or security process.
Common Process Injection Techniques
While the general steps remain the same, there are many techniques malware leverages to perform process injection. Some common ones include:
- DLL Injection – Inserts a malicious DLL into the target process. The DLL’s code gets executed in the target process address space.
- Memory Module Injection – Similar to DLL injection, but injects an in-memory DLL instead of a file on disk. Harder to detect.
- Thread Execution Hijacking – Forces the main thread of a process to load malicious code.
- Asynchronous Procedure Calls – Triggers APC calls to execute malicious payloads in the context of a thread.
- Thread Local Storage – TLS callbacks used to trigger malicious code when a thread is created.
- Import Address Table – Hooks API calls by patching the process’s import table.
- Reflective DLL Injection – Injects a DLL from memory into a process without writing any data to disk.
Attackers are continuously evolving these techniques to better evade modern defenses.
Why Attackers Choose Process Injection
There are several advantages for threat actors in utilizing process injection:
- Stealth – Running under a legitimate process makes the malware execution highly discreet. It evades techniques that detect new malicious processes.
- Trust – Inheriting the permissions of a trusted system process gives the malware privileged access to OS resources.
- Bypasses Protection – Modern defenses like antivirus, firewalls etc. often exclude monitoring system processes.
- Difficult Detection – Lack of malicious process creation and seamless execution makes process injection very hard to identify.
- Flexibility – Numerous techniques allow malware tailored injection with rapid testing to find what’s most effective.
For these reasons, process injection continues to be a staple technique in sophisticated cyber attacks.
Defending Against Process Injection Attacks
While process injection can be stealthy and complex, the following best practices can help strengthen defenses:
- Privileged Access Control – Limit processes that can be injected into using access control policies. Reduce attack surface.
- Memory Protection – Prevent execute permissions for memory sections susceptible to code injection like heap and stacks.
- Behavior Monitoring – Analyze process behavior anomalies like unusual child processes and code injections in real-time.
- Threat Intelligence – Identify Indicators of Compromise (IOCs) of known injection techniques to detect attacks.
- Endpoint Detection – Leverage advanced EDR solutions that can reveal sophisticated process injections across the kill chain.
- Proactive Hardening – Utilize tools like Enhanced Mitigation Experience Toolkit (EMET) to proactively block process injections.
With greater awareness of process injection and by adopting these best practices, organizations can significantly strengthen their defenses against these infiltration attacks in the cybersecurity arms race.
Process Hollowing: Deceptive Code Replacement
Process hollowing is an insidious code injection technique used by malware to evade detection by masquerading as legitimate system processes. In this section, we will unravel what process hollowing is, how it works, how it differs from process injection, and most importantly – how to defend systems against this stealthy attack.
What is Process Hollowing?
Process hollowing refers to a method where the memory of a legitimate system process is replaced with malicious code. The original process is hollowed out and continues running surreptitiously under its original context, disguising the execution of embedded malicious code.
This allows the malware to inherit the permissions of a critical OS process while avoiding behaviors that could reveal its presence. Process hollowing thereby enables adversaries to hide in plain sight.
How Process Hollowing Works: A Step-by-Step Guide
Here are the typical steps in a process hollowing attack:
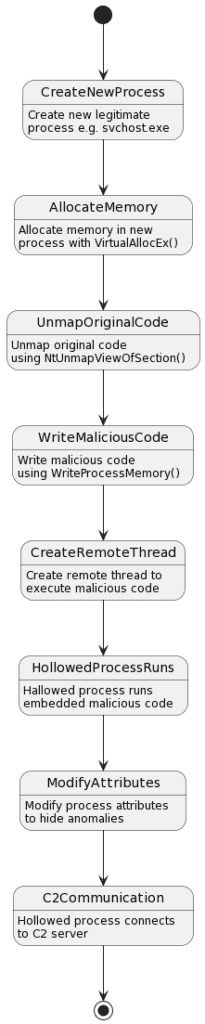
- Create a new instance of a legitimate process such as
svchost.exeorrundll32.exe. - Allocate memory in the new process with
VirtualAllocEx()ensuring the memory region has execute permissions. - Unmap the memory of the legitimate process using
NtUnmapViewOfSection()so the original code is inaccessible. - Write the malicious code into the allocated memory region using
WriteProcessMemory(). - Create a remote thread in the hollowed process to execute the injected code using
CreateRemoteThread(). - The hallowed process now runs the embedded malicious code clandestinely. The process’s attributes are modified to hide any anomalies.
- The hollowed process connects back to the attacker’s command-and-control server to carry out the adversary’s objectives.
By hijacking a legitimate process in this way, the malware manages to bypass security defenses and achieve persistence on the compromised system.
How Process Hollowing Differs from Process Injection?
While process hollowing and process injection are both methods to sneakily execute malicious code, there are some key differences:
- Process Creation – Hollowing creates a new instance of a process while injection targets an existing one.
- Degree of Intrusion – Hollowing replaces the entire process memory while injection leaves the original code.
- Stealth – Hollowing is stealthier as the process runs its original entry point.
- Persistence – Hollowed processes reconnect better after reboots providing persistent access.
- Memory Footprint – Injection has lower memory impact compared to hollowing’s memory unmapping.
So in summary, hollowing is focused on disguising malware as a legitimate executable while injection is about infiltrating malicious code into a running process.
Defending Against Process Hollowing Attacks
Process hollowing can be extremely difficult to detect due to its elusive nature. Here are some defensive strategies:
- Memory Protections – Prevent execute permissions for memory pages susceptible to code injection.
- Behavior Monitoring – Analyze processes for suspicious activities like hollowed memory and tampered execution flows.
- Authentication Enforcement – Validate legitimacy of system binaries and RAM maps via digital signatures and certificates.
- Threat Intelligence – Use IOCs to detect known hollowing techniques like usage of particular memory APIs.
- Hardening – Restrict processes from creating child processes or interacting with others via access control policies.
- Advanced EDR – Deploy endpoint security with artificial intelligence capabilities to identify anomalous behaviors.
With greater focus on process-level activity monitoring, rapid response, and advanced threat hunting – organizations can counter sophisticated attacks like process hollowing.
Process Doppelgänging: An Evasive Malware Technique
Process doppelgänging is an advanced code injection technique that allows malware to disguise itself as a legitimate process to stealthily execute on compromised systems. In this section, we unpack what process doppelgänging is, how it works, how it differs from other techniques, and strategies to detect and prevent doppelgänging attacks.
What is Process Doppelgänging?
Process doppelgänging is a fileless code injection technique leveraged by malware to evade security defenses. It involves spawning a malicious process that impersonates a legitimate system process, tricking the OS into believing the malware is the real process.
The name comes from the German folklore of a doppelgänger – a lookalike or double of a living person. Similarly, the malicious process pretends to be the legitimate process it is impersonating to hide in plain sight.
By masquerading as trusted system processes, doppelgänging bypasses techniques that detect malicious processes, allowing adversaries to surreptitiously gain persistence on target systems.
It allows attackers to execute malicious code in the context of a legitimate process by taking advantage of built-in Windows functions, specifically the NTFS transactional features. The primary allure for attackers using Process Doppelganging is that it can bypass most modern antivirus and forensic tools.
How Process Doppelgänging Works: A Step-by-Step Guide
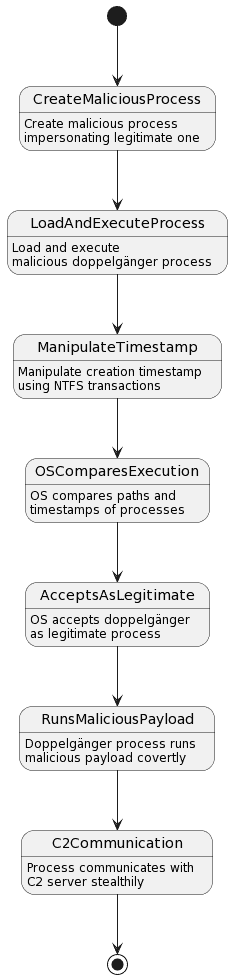
Here are the typical steps used in process doppelgänging attacks:
- A malicious executable is created, often given the same name as a legitimate process such as
svchost.exe. - The malicious process is loaded into memory and executed.
- Using NTFS transactions, the creation timestamp of the malicious process is modified to match the legitimate system process it is impersonating.
- When the OS compares the file paths and timestamps, it sees the doppelgänger as the real process and allows execution.
- The doppelgänger process now runs its malicious payload clandestinely while appearing legitimate to the OS.
- The process often utilizes stealth techniques to communicate back to the attacker avoiding further detections.
By abusing NTFS transactions in this manner, malware manages to disguise its identity and bypass many security defenses.
How Does it Differ from Other Techniques?
While process injection and hollowing also stealthily execute code, doppelgänging has some notable differences:
- It spawns a completely new process rather than using existing ones.
- The technique does not inject or hollow any processes, it impersonates them.
- There is no manipulation of memory or threads of other processes.
- It abuses filesystem artefacts instead of memoryinjections.
- Doppelgänging is fileless and leaves minimal traces on the filesystem itself.
These attributes allow doppelgänging to be exceptionally stealthy and resistant to many modern security tools.
Strategies to Detect and Prevent Doppelgänging
Defending against process doppelgänging requires a combination of these security strategies:
- Behavior monitoring – Analyze processes for anomaly detection based on activities and behaviors.
- Authentication – Verify legitimacy of system binaries via certificates and signatures to detect fakes.
- Filesystem monitoring – Monitor NTFS transactions for signs of timestamp tampering of executables.
- Memory analysis – Detect reflective injection techniques used to load doppelgänger processes.
- Block at load – Use protections like the Process Doppelgänging Mitigation tool that prevent phantom process loads.
- Advanced machine learning – Leverage AI and big data to identify patterns of malicious impersonation behavior.
- Threat intelligence – Use known IOCs and YARA rules to detect common doppelgänging techniques.
With greater vigilance and adoption of these security strategies, organizations can thwart the advanced evasion tactics like process doppelgänging.
How Three Process Attacks Differ Each Other?
Relative Threat Levels
Process injection is moderately dangerous because while malicious, it is injecting code into an existing process making it somewhat detectable.
Process hollowing is highly dangerous as it creates new malicious processes impersonating legitimate critical system processes. Very stealthy.
Process doppelgänging is the most dangerous as it is a fileless technique that fully impersonates a legitimate process making it extremely stealthy and undetectable.
Process Injection
- Threat Level: Moderate
- Injects code into running processes
- Somewhat detectable as new code in process
- Lower privilege escalation as just piggybacks off the existing process
Process Hollowing
- Threat Level: High
- Creates new malicious processes impersonating legitimate ones
- Very stealthy as legit process exterior is maintained
- Gains elevated privileges of impersonated critical process
- Difficult to detect hollowed process memory
Process Doppelgänging
- Threat Level: Very High
- Creates new malicious process mimicking legitimate process
- Fileless method, extremely difficult to detect
- Manipulates process metadata to impersonate trusted process
- Gains highest privileges while fully stealthy
Process Injection vs. Process Hollowing vs. Process Doppelganging
Process Injection:
- Involves injecting malicious code into a running process. The existing process is not killed.
- Exploits the execution flow of an existing process to hide the malicious code.
- Common injection methods are remote DLL injection, thread hijacking, etc.
- Can be detected by monitoring unusual modules loaded by processes.
Process Hollowing:
- Creates a new instance of a legitimate process like svchost.exe.
- The malicious code deallocates the original process’s memory and overwrites it with malicious code.
- The hijacked process retains the execution flow of the original process it impersonated.
- Difficult to detect as the exterior of the legitimate process is maintained.
Process Doppelgänging:
- Similar to hollowing but does not use any injection or hollowing techniques.
- A malicious process impersonates a legitimate process by name.
- Uses NTFS transactions to modify the doppelgänger’s creation timestamp to match a legitimate process.
- Completely evades defenses that detect malicious processes as it impersonates a legitimate one.
In summary – injection leverages running processes, hollowing creates impersonators, and doppelgänging utilizes fileless techniques to masquerade as legitimate processes. Understanding these differences allows selecting the appropriate defenses against each technique.
Conclusion
As cyberattacks grow more advanced, malware authors have developed ingenious techniques to bypass modern security defenses. Process-based attacks exploit weaknesses in how operating systems manage processes to camouflage malicious code.
Process injection involves injecting code into legitimate processes to hide malicious activity in plain sight. Common injection methods like DLL injection and thread hijacking allow malware toblend in with normal system operations. Though moderately detectable, process injection grants adversaries a covert channel for infiltration.
Even more deceptive is process hollowing where malware creates new processes impersonating legitimate ones like svchost.exe. By replacing the process’s memory with malicious code while retaining the original flow, malware achieves high privileges with minimal detection.
The most sophisticated of such attacks is process doppelgänging. This utilizes fileless techniques to create malicious processes mimicking legitimate ones via process metadata manipulation. Entirely camouflaged from defenses that detect malicious processes, doppelgänging represents the pinnacle of stealthy process masquerading attacks.
Defending against such techniques requires focusing on anomaly detection, memory protections, endpoint security with advanced machine learning capabilities, and rapid incident response. By understanding the motivations and methods of attacks like process injection, hollowing and doppelgänging, organizations can select appropriate countermeasures to harden systems.
Though adversaries continue to evolve increasingly stealthy attacks, vigilant defenders can protect assets by adopting a proactive cybersecurity posture and response strategy based on assumption of breach. With diligence and adapting to the ever-changing threat landscape, enterprises can secure their critical business interests against sophisticated cyberattacks.




