Are you a tech enthusiast or penetration tester looking for a versatile and powerful tool to increase your efficiency? Then Flipper Zero could be the best option for you. It’s the ultimate multi-tool that provides comprehensive coverage of digital vulnerabilities, making it the perfect choice for identifying weaknesses in digital systems. With features such as SIM card emulation, hardware hacking capabilities, and open source firmware, this portable Swiss Army knife of antennas is designed to help security professionals find vulnerabilities in various types of wireless networks as well as cover up your tracks post-attack and stay ahead of cyber attacks. Let’s see why the Flipper Zero is a must to have hacking tool for penetration testers and security enthusiasts.
What is Flipper Zero?
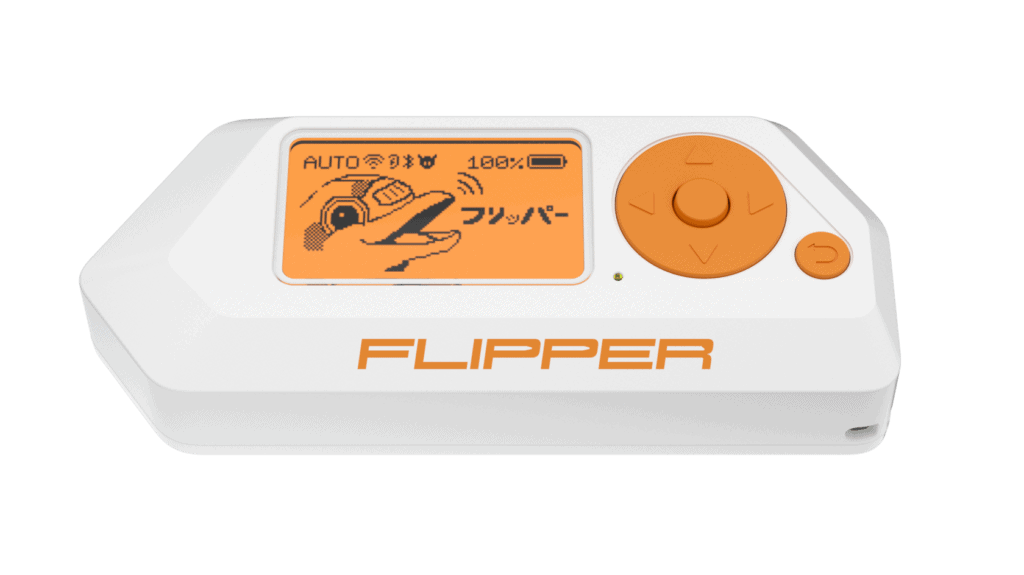
Flipper Zero is a powerful, multi-functional tool designed for serious tech enthusiasts and security professionals. It allows users to quickly interact with physical access control systems, RFID tags, NFC tags, and other mechanisms from one handy device. It can be used to identify weaknesses and vulnerabilities in digital systems, making it an ideal choice for penetration testing.
Its capabilities include SIM card emulation for GSM-based attacks, hardware and software hacking using wireless connections such as WiFi or Bluetooth, open-source firmware for customizations like tethering a device to another computer without having access to its physical ports, support for various hardware interfaces allowing direct access into otherwise secured devices by attacking their physical controls directly onsite with many conveniences — all this wrapped up in a portable form factor offering the on-the-go capability of testing anytime according to need.
The Flipper Zero comes packed with capable hardware, such as a large infrared sensor that can control home automation equipment like TVs, air conditioners, and music systems.
The device can also read, copy, clone, or emulate both 125kHz (low frequency) and 13.56MHz (high frequency) RFID/NFC cards or badges, which have become ubiquitous in offices worldwide as access control tools over recent years.
In addition to its diminutive size, convenient portability, plus extended battery life – up to 10 hours when using Bluetooth–the Flipper Zero runs a comprehensive set of opensource pentesting programs out-of-the-box in order to scan networks without needing additional downloads, making it ideal for conducting quick scans whilst away from the office.
Key Features of Flipper Zero:
Flipper Zero boasts several key features that make it a versatile and powerful tool for interacting with access control systems. Some of its main features include:
- RFID and NFC tags: Flipper Zero can read, copy, and emulate a variety of RFID and NFC tags, allowing users to easily interact with different access control systems using these technologies.
- Radio remotes: The device can also work with radio remotes, making it a handy tool for interacting with various wireless systems.
- iButton compatibility: Flipper Zero supports iButton, a type of electronic key used in access control systems, enabling users to read, copy, and emulate these keys.
- Digital access keys: With its ability to interact with digital access keys, Flipper Zero can be used with a wide range of access control systems, such as door locks and other security systems.
- GPIO interface: Flipper Zero includes a general-purpose input/output (GPIO) interface, which allows for further customization and interaction with other devices and systems.
Technical Specifications of Flipper Zero:
Let’s delve into the technical specifications, hardware, and firmware of the Flipper Zero, a must-have hacking tool for penetration testers.
Hardware Specifications:
Compact design, featuring a 1.4-inch 128×64 LCD monochrome display, a 5-button joystick with a back button, and a 2000mAh rechargeable battery. This device packs a range of functionalities, including support for Sub-1 GHz frequencies, 13.56 MHz NFC, 125 kHz RFID, 18 GPIO connectors, infrared communication, and iButton 1-Wire compatibility. The Flipper Zero also includes a USB 2.0 Type-C port for charging and connectivity.
Flipper Zero is equipped with two processors, ARM Cortex-M4 32-bit 64 MHz (application processor) and ARM Cortex-M0+ 32 MHz (network processor). Both are used to perform a variety of hardware exploration, firmware flashing, debugging, and fuzzing tasks.
The Flipper Zero is designed to support a wide range of communication protocols, including Sub-1 GHz frequencies (315 MHz, 433 MHz, 868 MHz, and 915 MHz, depending on region), 13.56 MHz NFC, and 125 kHz RFID.
In addition to its RF capabilities, the Flipper Zero offers infrared (TX/RX range: 800-950 nm, TX power: 300 mW) and iButton 1-Wire support (Dallas DS1990A/CYFRAL compatible). These features expand the device’s potential applications and compatibility with a diverse range of systems.
Its RF chipset, the TI CC1101, supports multiple frequency bands and has a maximum transmit power of 0 dBm. The device’s RFID module is compatible with both high-frequency (13.56 MHz) and low-frequency (125 kHz) cards, offering support for various protocols and card types. Additionally, the Flipper Zero includes 3.3V CMOS-level GPIO connectors, an infrared communication module, and Bluetooth LE 5.0 connectivity.
With dimensions of 100 x 40 x 25 mm and a weight of just 102g, the Flipper Zero is designed for easy transport and everyday use. Its compact size and lightweight construction makes it an essential addition to any tech enthusiast’s toolkit.
- Screen: 128×64 1.4″ LCD Monochrome (Backlit)
- Tactile Controls: 5-Way Direction Pad + Select Button
- Internal Battery: LiPo 2000mAh (7-days without charge)
- CPU:
- STM32WB55RG
- ARM Cortex-M4 32-bit 64 MHz (Application Processor)
- ARM Cortex-M0+ 32 MHz (Network Processor)
- Buzzer: 100-2500Hz
- Vibration Motor
- Memory: 1024KB Flash, 256KB SRAM
- Storage: MicroSD (Up to 64GB)
- Connectivity: USB 2.0, Type-C
- Dimensions: 100 x 40 x 25 mm
- Weight: 102g
- RF:
- Chipset: TI CC1101
- Frequency bands: 315MHz, 433MHz, 868MHz, 915MHz
- TX Power: 0dBm Max (~100m transmit range)
- RFID:
- High Frequency / 13.56MHz
- ISO-14443A/B
- NXP Mifare® Classic/Ultralight/DESFire/etc
- FeliCa™
- NFC Forum protocols
- Low Frequency / 125KHz
- Modulation: AM / PSK / FSK
- Supported Cards: EM400x, EM410x, EM420x
- HIDProx, Indala
- T5577
- High Frequency / 13.56MHz
- GPIO:
- 3.3v CMOS Level
- 5V tolerant
- Up to 20mA per digital pin
- Infrared:
- RX/TX Frequency: 800-950nm
- TX Power: 300 mW
- Bluetooth:
- Bluetooth LE 5.0
- TX Power: 0dBm Max
- RX Sensitivity: -96dBm
- Data Rate: 2 Mbps
- iButton 1-Wire:
- Dallas DS1990A
- CYFRAL
Software Specifications:
The Flipper Zero firmware is built upon the FreeRTOS operating system. Primarily coded in the C programming language, the firmware occasionally utilizes C++ for third-party modules.
Key Components of the Flipper Zero Firmware:
- FuriCore: Serving as the backbone for scheduler and multithreading interaction, FuriCore offers an API that abstracts and extends the functionality of the FreeRTOS scheduler. It also introduces additional system primitives for enhanced performance.
- FuriHal: Delivering an API for seamless hardware interaction, FuriHal is integral to the firmware’s overall functionality.
- Services and Applications: Representing the device’s core functionality, services and applications include Sub-GHz, Infrared, RFID, NFC, and more for user interaction. Additional APIs, such as the Graphical User Interface (GUI), Command-Line Interface (CLI), Notification, Storage, and others, are provided for application development.
- Libraries and Drivers: The firmware boasts a comprehensive set of libraries and drivers, encompassing communication protocols, device drivers, file system drivers, and various developer tools.
Why Flipper Zero Is A Must-Have Hacking Tool For Penetration Testers?
Flipper Zero is an essential and highly useful tool for professional penetration testers. It is a pocket-sized portable device packed with a range of sensors, chips, antennas, and many other features that make it a Swiss Army knife of hacking tools.
See Also Understanding Indicator Of Compromise (IoC)
This multifunctional device can be used to emulate previously scanned fobs, explore hardware components of digital stuff, flash the firmware on IoT devices, and debug software applications as well as bad USB devices, among others.
It has become increasingly popular in the tech community since its launch due to its portability and multifunctional capabilities, which makes it a great option for those who are looking for alternative pentesting tools or hacker toys at reasonable price points compared to Raspberry Pi hardware or expensive programmer boards such as Flipper One.
It allows penetration testers to interact with a variety of devices and access control systems.
- RFID and NFC-based access control systems: Flipper Zero can read, copy, and emulate RFID and NFC tags, making it compatible with devices using these technologies for access control.
- Radio remotes: The device can work with radio remotes, enabling users to control various wireless systems, such as garage doors or alarm systems.
- iButton devices: Flipper Zero supports iButton, a type of electronic key often used in asset control and tracking. This allows users to interact with devices that utilize iButton technology.
- Sub-1GHz Transceiver: Flipper antenna allows it to interact with old-fashioned devices such as garage doors, restaurant pagers, gates, gas station price signs, and doorbells.
- Devices support 125kHz Antenna: Flipper antenna allows you to read, clone, and emulate older prox cards.
- Infrared Transceiver: It lets you learn any IR device on the fly. If you lose the remote to your air conditioner or sound bar in a move, the Flipper antenna can learn how to control it. It’s even possible that someone else has already figured out the code for the device you need to control.
- USB Devices: By connecting the Flipper device to a computer via USB, users can run various Ducky Scripts, enabling them to execute BadUSB attacks.
- U2F Keys Storage: By connecting the Flipper device to a computer via USB, users can run various Ducky Scripts, enabling them to execute BadUSB attacks.
- Working over WiFi network: Although the Flipper device does not have built-in WiFi, users can quickly enhance its capabilities by adding a WiFi Devboard or ESP8266 to the GPIO pins. This enables pentesters to work over WiFi networks.
Additionally, Flipper Zero features 18 general-purpose input/output (GPIO) connectors that can connect it to other hardware devices, a USB 2.0 Type-C port for computer connectivity, and removable storage in the form of an SD card. These features further expand the range of devices and systems that Flipper Zero can interact with and control.
Things can be done with Flipper Zero:
- Taking over TVs with Flipper Zero Infrared Port
- Flipper Zero as a password manager
- Flipper Zero as a universal remote control
- Flipper Zero as a wireless keyboard, mouse, and touchpad
- Flipper Zero as a wireless game controller and joystick
- Flipper Zero as a wireless media controller
- Flipper Zero as a car key unlocker
- Flipper Zero as an access card
Is Flipper Zero Legal to Use?
The legality of using Flipper Zero depends on the specific laws and regulations in your country or region, as well as the manner in which you use the device. In general, using Flipper Zero for educational purposes, personal projects, or ethical penetration testing to identify and fix security vulnerabilities in systems you have permission to access is usually considered legal.
However, using Flipper Zero to gain unauthorized access to systems, steal data, or commit other illegal activities is strictly against the law. It is essential to understand the legal boundaries in your area and ensure that you use the device responsibly and ethically.
Is Flipper Zero Legal to Use in the United States?
However, it is important to note that the legality of using Flipper Zero in the United States also depends on the purpose and manner in which you use the device. If you use it for educational purposes, personal projects, or ethical penetration testing on systems you have permission to access, its use is generally considered legal. Using Flipper Zero for illegal activities, such as unauthorized access to systems or data theft, is against the law.
See Also What Does Happen Inside the Tor Network? | How Does the Tor Network Work?
To ensure you are using Flipper Zero legally, always follow relevant laws and regulations, and use the device responsibly and ethically.




