On 17th Feb 2022, the Qualys Research Team published a post that says the research team has identified multiple vulnerabilities in the snap-confine function, a program used in Snap package manager to construct the execution environment for snap applications. The team says the vulnerability, tracking as CVE-2021-44731, is the most critical of all in the list, which can be abused to perform privilege escalation attacks and obtain full root privileges on the default installation of Debian/Ubuntu Linux distributions. The flaw has got a score of 7.8 in the CVSS scoring system and is categorized as High. It is important to Fix the CVE-2021-44731 vulnerability. We have created this post to let you know how to fix the CVE-2021-44731 (Oh Snap!) vulnerability- A privilege escalation vulnerability in the Snap package manager.
What Are Snap Package Manager, Snaps, Snapd, And Snap-confine?
Snap package manager is a well knows software packaging and development system developed for an operating system that uses Linux kernel. The ultimate goal behind creating the Snap package manager is to reduce the dependency issues commonly seen in package installations in Linux distributions by creating application snaps including the dependent libraries. In Snap package manager system, the created application packages are called snaps, and the tool for using those application snaps is called snapd. Snaps are self-contained applications with all the required dependency packages to run the application. Snaps runs the applications in a sandbox with mediated access to the host system. Snap-confine is a program in snapd used to construct the execution environment for snap applications.
Snap package manager was created by Canocical, a UK-based private computer software company. Initially, Snap was developed for cloud applications, later it was introduced to IoT devices and desktop Linux distributions, and now for applications too.
“A race condition existed in the snapd 2.54.2 snap-confine binary when preparing a private mount namespace for a snap. This could allow a local attacker to gain root privileges by bind-mounting their own contents inside the Snap’s private mount namespace and causing snap-confine to execute arbitrary code and hence gain privilege escalation.”
| Associated CVE ID | CVE-2021-44731 |
| Description | A Privilege Escalation Vulnerability in Snap Package Manager |
| Associated ZDI ID | – |
| CVSS Score | 7.8 High |
| Vector | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H |
| Impact Score | 6.0 |
| Exploitability Score | 1.1 |
| Attack Vector (AV) | Local |
| Attack Complexity (AC) | High |
| Privilege Required (PR) | Low |
| User Interaction (UI) | None |
| Scope | Changed |
| Confidentiality (C) | High |
| Integrity (I) | High |
| availability (a) | High |
Summary Of Other Vulnerabilities Disclosed With Snap-Confine Local Privilege Escalation Vulnerability:
There are other six vulnerabilities disclosed in Snap. Here you can see the list of the vulnerabilities:
| CVE ID | Base Score | Short Description | CVSS Vector |
| CVE-2021-44730 | 7.8 High | Hardlink attack in snap-confine’s sc_open_snapd_tool() | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:C/C:H/I:H/A:H |
| CVE-2021-3996 | 5.5 Medium | Unauthorized unmount in util-linux’s libmount | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H |
| CVE-2021-3995 | 4.7 Low | Unauthorized unmount in util-linux’s libmount | CVSS:3.1/AV:L/AC:H/PR:L/UI:N/S:U/C:N/I:N/A:H |
| CVE-2021-3998 | 5.9 Medium | Unexpected return value from glibc’s realpath() | CVSS:3.1/AV:N/AC:H/PR:N/UI:N/S:U/C:H/I:N/A:N |
| CVE-2021-3999 | 7.4 High | Off-by-one buffer overflow/underflow in glibc’s getcwd() | CVSS:3.1/AV:L/AC:H/PR:N/UI:N/S:U/C:H/I:H/A:H |
| CVE-2021-3997 | 5.5 Medium | Uncontrolled recursion in systemd’s systemd-tmpfiles | CVSS:3.1/AV:L/AC:L/PR:L/UI:N/S:U/C:N/I:N/A:H |
PoC Of CVE-2021-44731 (Oh Snap!)- A Privilege Escalation Vulnerability In Snap Package Manager
Qualys confirmed that their research team has independently verified the vulnerability by developing an exploit for the CVE-2021-44731 vulnerability and obtaining full root privileges on default installations of Ubuntu. However, Qualys also confirmed that they hadn’t published the exploit code on public forums to avoid exploitation of the flaw. They just published a video note that shows the evidence of the Privilege Escalation Vulnerability in Snap Package Manager.
How To Detect CVE-2021-44731 (Oh Snap!)?
There is no such code or script to detect the CVE-2021-44731 vulnerability. Either you should use Vulnerability scanning tools like Qualys VMDR or check the version of Snap package installed on your Linux servers.
Use the following command on the respective Linux distributions to check the installed version of Snapd. If you see the snapd version less than or equal to v2.54.2, then that Linux server is vulnerable to the Snap-Confine Local Privilege Escalation Vulnerability.
| Linux Distribution | Command to check the Snapd version |
| Ubuntu / Debian / Linux Mint | sudo apt list snapdORsudo apt info snapdORsudo dpkg -l snapd |
| Red Hat Enterprise / Cent OS | sudo yum list snapdORsudo yum info snapdORrpm -qi snapd |
| Fedora | sudo dnf list snapdORsudo dnf info snapd |
| Arch Linux | pacman -Qi snapd |
| Alpine Linux | apk info snapd |
| SUSE Linux | zypper se -s snapdORrpm -qi snapd |
How To Fix CVE-2021-44731- A Privilege Escalation Vulnerability In Snap Package Manager?
Qualys security team reported the vulnerability to the both Vendor and Open Source distributions on October 27, 2021. In response to that, Ubuntu and other Linux distributions have released the patches on February 17 as part of a coordinated disclosure process.
Snap v2.54.2 or lesser is vulnerable to the Snap-Confine Local Privilege Escalation Vulnerability. You should upgrade to v2.54.3 and above to fix the CVE-2021-44731 vulnerability.
How to Fix the CVE-2021-44731- A Privilege Escalation Vulnerability in Snap Package Manager?
- Verify the snapd version
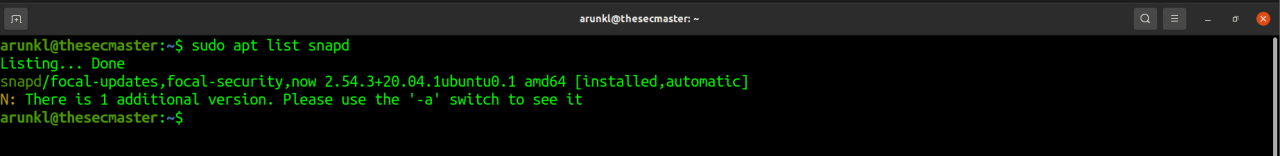
Run this command to check the snapd version on a Ubuntu server.
$ sudo apt list snapd
In this case, we have snapd v2.51.1 which can be upgradable to v2.54.3. - Update the repositoryRun this command to update the repository.
$ sudo apt update - Upgrade the snapdRun this command to upgrade only snapd
$ sudo apt install snapd=2.54.3+20.04.1ubuntu0.1
OR
Run this command to upgrade all the packages. We recommend this approach as it is good to keep all the packages up to date.
$ sudo apt upgrade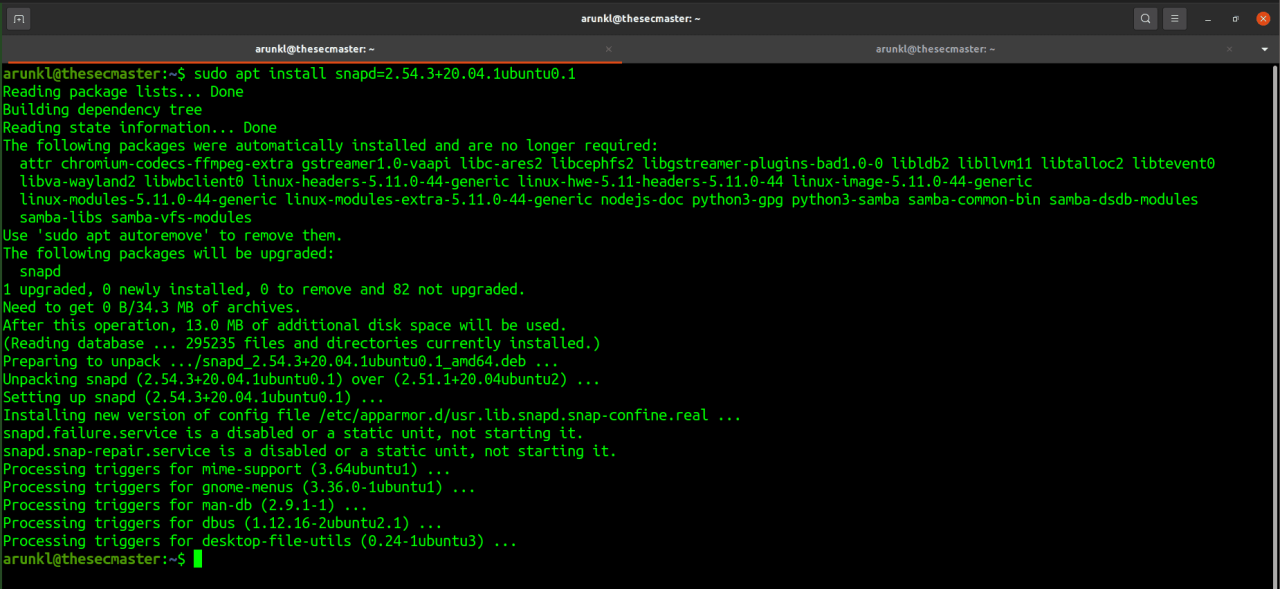
- Check the snapd versionCheck the snapd version as shone in the first step. Run this command to check the snapd version on a Ubuntu server.
$ sudo apt list snapd